| How to find: Press “Ctrl + F” in the browser and fill in whatever wording is in the question to find that question/answer. If the question is not here, find it in Questions Bank. |
|
NOTE: If you have the new question on this test, please comment Question and Multiple-Choice list in form below this article. We will update answers for you in the shortest time. Thank you! We truly value your contribution to the website.
|
CyberOps Associate (Version 1.0) – Modules 1 – 2: Threat Actors and Defenders Group Exam Answers
1. Which personnel in a SOC is assigned the task of verifying whether an alert triggered by monitoring software represents a true security incident?
- Tier 1 personnel
- Tier 2 personnel
- Tier 3 personnel
- SOC Manager
2. After a security incident is verified in a SOC, an incident responder reviews the incident but cannot identify the source of the incident and form an effective mitigation procedure. To whom should the incident ticket be escalated?
- the SOC manager to ask for other personnel to be assigned
- an alert analyst for further analysis
- a cyberoperations analyst for help
- a SME for further investigation
3. Which two services are provided by security operations centers? (Choose two.)
- responding to data center physical break-ins
- monitoring network security threats
- managing comprehensive threat solutions
- ensuring secure routing packet exchanges
- providing secure Internet connections
4. Which organization is an international nonprofit organization that offers the CISSP certification?
- CompTIA
- (ISC)2
- IEEE
- GIAC
5. What is a benefit to an organization of using SOAR as part of the SIEM system?
- SOAR was designed to address critical security events and high-end investigation.
- SOAR would benefit smaller organizations because it requires no cybersecurity analyst involvement once installed.
- SOAR automates incident investigation and responds to workflows based on playbooks.
- SOAR automation guarantees an uptime factor of “5 nines”.
6. Which personnel in a SOC are assigned the task of hunting for potential threats and implementing threat detection tools?
- Tier 3 SME
- Tier 2 Incident Reporter
- Tier 1 Analyst
- SOC Manager
7. An SOC is searching for a professional to fill a job opening. The employee must have expert-level skills in networking, endpoint, threat intelligence, and malware reverse engineering in order to search for cyber threats hidden within the network. Which job within an SOC requires a professional with those skills?
- Incident Responder
- Alert Analyst
- SOC Manager
- Threat Hunter
8. Which three are major categories of elements in a security operations center? (Choose three.)
- technologies
- Internet connection
- processes
- data center
- people
- database engine
9. Which KPI metric does SOAR use to measure the time required to stop the spread of malware in the network?
- MITR
- Time to Control
- MITC
- MTTD
The common key performance indicator (KPI) metrics compiled by SOC managers are as follows:
• Dwell Time: the length of time that threat actors have access to a network before they are detected and the access of the threat actors stopped
• Mean Time to Detect (MTTD): the average time that it takes for the SOC personnel to identify that valid security incidents have occurred in the network
• Mean Time to Respond (MTTR): the average time that it takes to stop and remediate a security incident
• Mean Time to contain (MTTC): the time required to stop the incident from causing further damage to systems or data
• Time to Control the time required to stop the spread of malware in the network
10. Which three technologies should be included in a SOC security information and event management system? (Choose three.)
- security monitoring
- threat intelligence
- proxy service
- firewall appliance
- intrusion prevention
- log management
Event collection, correlation, and analysis
Security monitoring
Security control
Log management
Vulnerability assessment
Vulnerability tracking
Threat intelligence
Proxy server, VPN, and IPS are security devices deployed in the network infrastructure.
11. The term cyber operations analyst refers to which group of personnel in a SOC?
- Tier 1 personnel
- Tier 3 personnel
- Tier 2 personnel
- SOC managers
12. How does a security information and event management system (SIEM) in a SOC help the personnel fight against security threats?
- by analyzing logging data in real time
- by combining data from multiple technologies
- by integrating all security devices and appliances in an organization
- by dynamically implementing firewall rules
13. What job would require verification that an alert represents a true security incident or a false positive?
- Alert Analyst
- Threat Hunter
- SOC Manager
- Incident Reporter
14. When a user turns on the PC on Wednesday, the PC displays a message indicating that all of the user files have been locked. In order to get the files unencrypted, the user is supposed to send an email and include a specific ID in the email title. The message also includes ways to buy and submit bitcoins as payment for the file decryption. After inspecting the message, the technician suspects a security breach occurred. What type of malware could be responsible?
- Trojan
- spyware
- adware
- ransomware
15. An employee connects wirelessly to the company network using a cell phone. The employee then configures the cell phone to act as a wireless access point that will allow new employees to connect to the company network. Which type of security threat best describes this situation?
- rogue access point
- cracking
- spoofing
- denial of service
16. Match the SOC metric to the description. (Not all options are used.)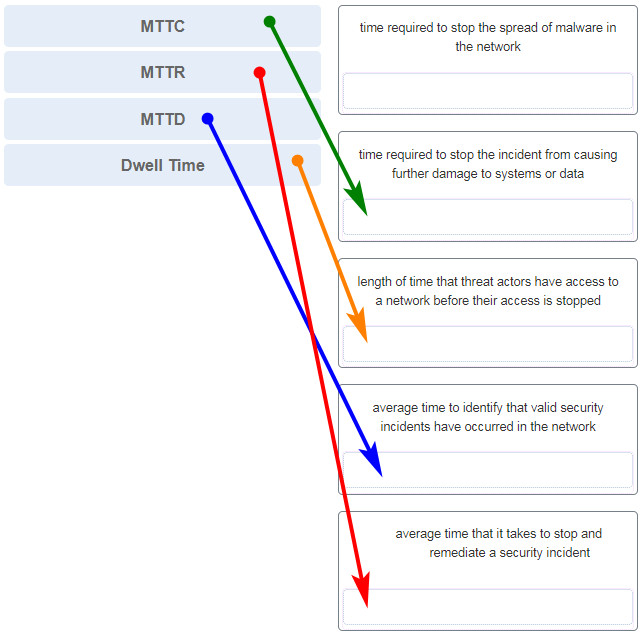
- Dwell Time
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Mean Time to Contain (MTTC)
- Time to Control
17. A group of users on the same network are all complaining about their computers running slowly. After investigating, the technician determines that these computers are part of a zombie network. Which type of malware is used to control these computers?
- botnet
- spyware
- virus
- rootkit
18. Which statement describes cyberwarfare?
- It is Internet-based conflict that involves the penetration of information systems of other nations.
- It is simulation software for Air Force pilots that allows them to practice under a simulated war scenario.
- Cyberwarfare is an attack carried out by a group of script kiddies.
- It is a series of personal protective equipment developed for soldiers involved in nuclear war
19. Why do IoT devices pose a greater risk than other computing devices on a network?
- Most IoT devices do not receive frequent firmware updates.
- Most IoT devices do not require an Internet connection and are unable to receive new updates.
- IoT devices cannot function on an isolated network with only an Internet connection.
- IoT devices require unencrypted wireless connections.
20. What are two examples of personally identifiable information (PII)? (Choose two.)
- first name
- IP address
- language preference
- street address
- credit card number
21. What is the dark web?
- It is a website that reports the most recent activities of cybercriminals all over the world.
- It is a website that sells stolen credit cards.
- It is part of the internet where a person can obtain personally identifiable information from anyone for free
- It is part of the internet that can only be accessed with special software.
22. A company has just had a cybersecurity incident. The threat actor appeared to have a goal of network disruption and appeared to use a common security hack tool that overwhelmed a particular server with a large amount of traffic. This traffic rendered the server inoperable. How would a certified cybersecurity analyst classify this type of threat actor?
- terrorist
- hacktivist
- state-sponsored
- amateur
23. A user calls the help desk complaining that the password to access the wireless network has changed without warning. The user is allowed to change the password, but an hour later, the same thing occurs. What might be happening in this situation?
- rogue access point
- password policy
- weak password
- user error
- user laptop
24. Which regulatory law regulates the identification, storage, and transmission of patient personal healthcare information?
- FISMA
- HIPAA
- PCI-DSS
- GLBA
25. A worker in the records department of a hospital accidentally sends a medical record of a patient to a printer in another department. When the worker arrives at the printer, the patient record printout is missing. What breach of confidentiality does this situation describe?
- EMR
- PII
- PSI
- PHI
26. Which cyber attack involves a coordinated attack from a botnet of zombie computers?
- DDoS
- MITM
- address spoofing
- ICMP redirect
27. What is the main purpose of cyberwarfare?
- to protect cloud-based data centers
- to develop advanced network devices
- to gain advantage over adversaries
- to simulate possible war scenarios among nations
28. What type of cyberwarfare weapon was Stuxnet?
- botnet
- virus
- worm
- ransomware
29. Which example illustrates how malware might be concealed?
- A hacker uses techniques to improve the ranking of a website so that users are redirected to a malicious site.
- An attack is launched against the public website of an online retailer with the objective of blocking its response to visitors.
- A botnet of zombies carry personal information back to the hacker.
- An email is sent to the employees of an organization with an attachment that looks like an antivirus update, but the attachment actually consists of spyware.
30. What websites should a user avoid when connecting to a free and open wireless hotspot?
- websites to check account fees
- websites to check product details
- websites to check stock prices
- websites to make purchases
31. In a smart home, an owner has connected many home devices to the Internet, such as the refrigerator and the coffee maker. The owner is concerned that these devices will make the wireless network vulnerable to attacks. What action could be taken to address this issue?
- Configure mixed mode wireless operation.
- Install the latest firmware versions for the devices.
- Assign static IP addresses to the wireless devices.
- Disable the SSID broadcast.
